Hi All,
I would like to go through the steps for installing and configuring an ADFS proxy server. ADFS proxies are used to put out on your perimeter network for remote internal users to access your ADFS farm from the internet without having to expose your ADFS server(s) to the outside. When an internal user accesses your network remotely, the ADFS Proxy will use forms based authentication to allow the user to enter their credentials. You will need to have at least one ADFS server installed to install a proxy. The proxy will also need an SSL certificate and its subject name must match the Federation Service Name. Your Federation proxy and your federation servers will resolve to the same Federation Service Name. Since one is internal and the other is external you will need to use a split brain DNS configuration or some other configuration so users will resolve to the ADFS Proxies when they are external to your network and resolve to the ADFS Server farm directly when they are on your internal network. For example, when a client is on the internal network and they try an access a claims aware application which redirects the browser to adfs.pipe2text.com the will go directly to the ADFS Server farm using Windows Authentication. If you have a remote internal user (user from your domain that is currently accessing from the Internet) that is accessing the same claims aware application which redirects their browser to adfs.pipe2text.com they will be redirected to the ADFS proxy which will use forms based authentication. In other words, both your ADFS Proxy (or Proxy Farm) and your ADFS Server (or ADFS Server Farm) would resolve as adfs.pipe2text.com.
Installing the ADFS 2.0 as a Proxy Server
You will need to download the latest version of ADFS 2.0 from Microsoft’s website. As of the writing of this article I had to download the ADFS install along with ADFS 2.0 Rollup 1. Rollup 1 includes some important fixes and enhancements so it is important that you install that as well especially if you have rollup 1 installed on your ADFS Servers. Be sure to download the correct version of the ADFS 2.0 install and rollup depending on whether the type of operating system have is Windows 2008 32 or 64 bit version or Windows 2008 R2. Do NOT install the role for ADFS role that is included in Windows as it is not the current version of ADFS. After you have downloaded the necessary files you can begin the install which is pretty much the same as when you install the software for an ADFS Server but you choose the proxy role instead. After the software is installed, it will then need to be configured.
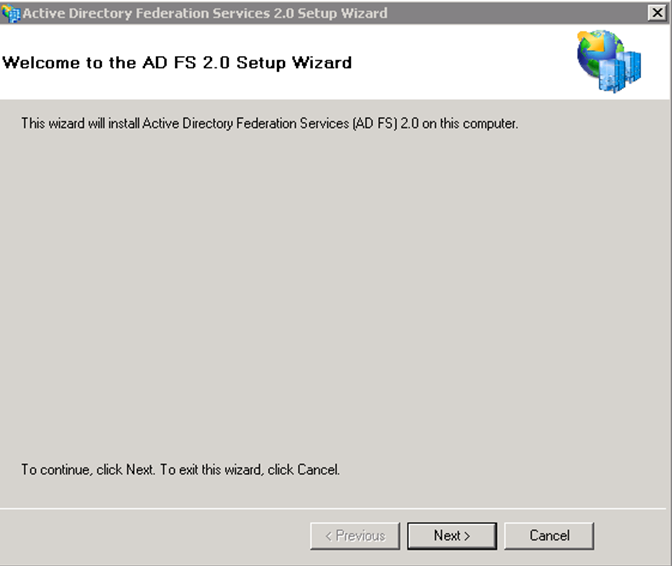
1. Run the executable that you downloaded from Microsoft’s website “ADFSSetup.exe”.
2. When the “Welcome to ADFS 2.0 Setup’ screen appears, Click “Next”.
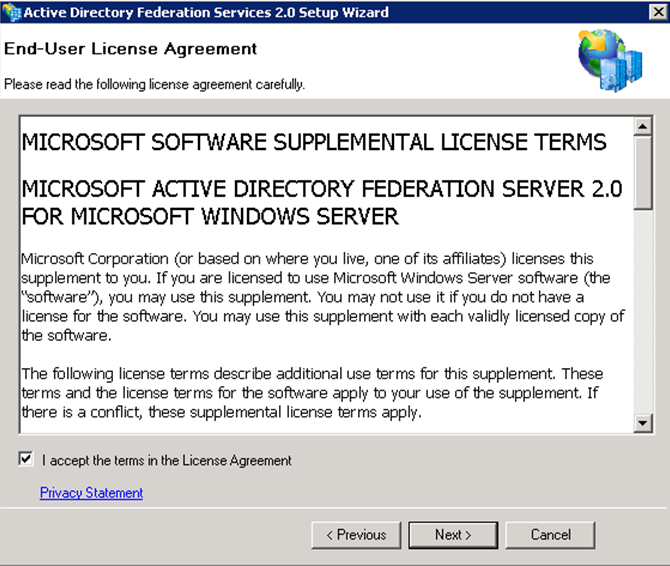
3. Accept the EULA agreement and Click “Next”.
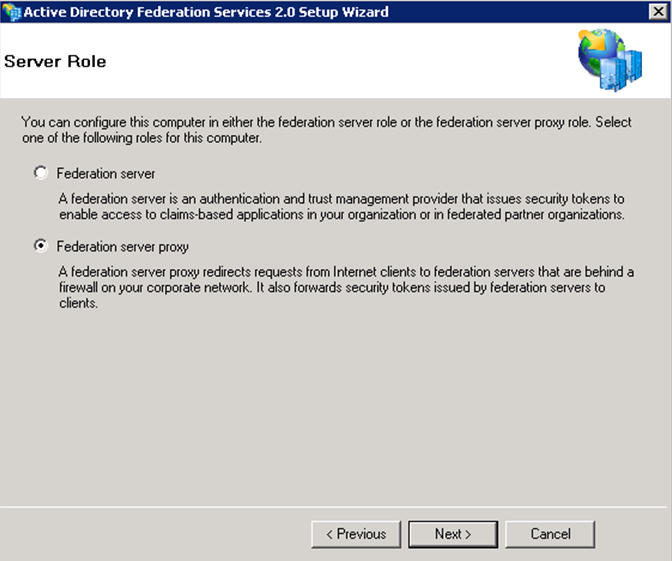
4. Choose the “Federation Proxy” role on the “Server Role” screen and Click “Next”.
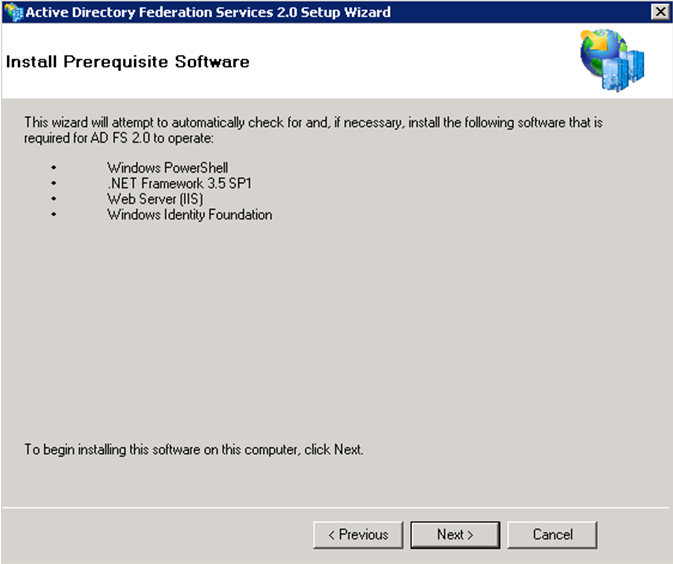
5. On the “Install Prerequisite Software” screen Click “Next” to install the required prerequisites for ADFS 2.0.
The Prerequisites and ADFS 2.0 will now begin to install as shown in the image below. Depending on the prerequisites needed, the time for the installation will vary.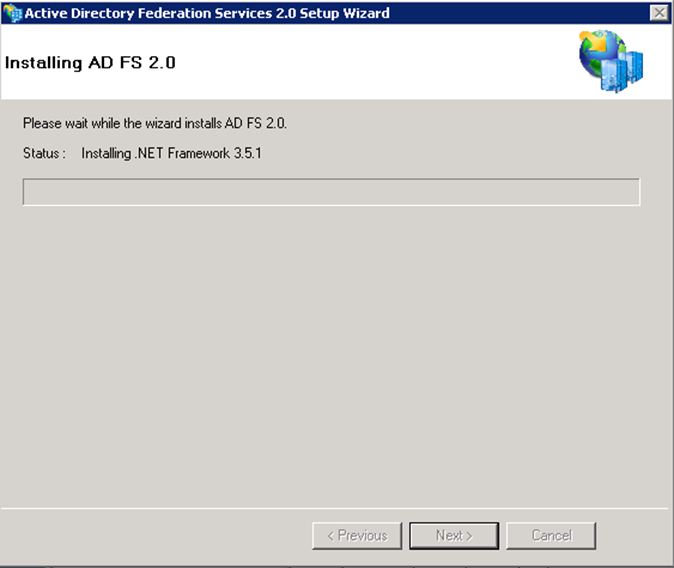
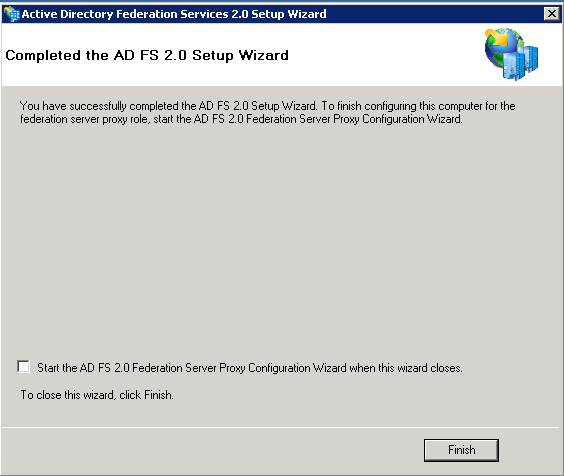
6. Once the install is completed you will receive a completion screen for the ADFS 2.0 Setup Wizard. You can choose to start the “ADFS 2.0 Management Snap-in” when the wizard closes but I have deselected it as I want to move on to installing ADFS 2.0 Rollup 1. Deselect the “Start the ADFS 2.0 Federation Proxy Wizard when this wizard closes” and click “Finish”.
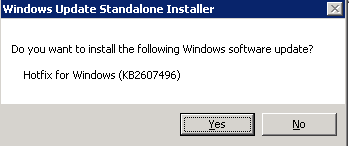
7. Run the installer for ADFS 2.0 Rollup 1 that you downloaded from Microsoft’s website and click “Yes” to install the update as shown below.
8. Click “Close” close when the install is complete.
At this point you have installed the ADFS Software for the Proxy Role. The next steps will be to configure the server using the ADFS Proxy Server Configuration Wizard.
Configuring the ADFS 2.0 Proxy Server
For the configuration wizard to start, you will need an SSL certificate and it you will need to bind it to the default website. If you do not do this, the configuration wizard will not run. Since I am setting this up in a lab I will be using a self signed cert. In a production scenario you would not use a self signed cert, you would need to get a certificate issued by a 3rd party CA such as Verisign that is trusted all machines that are accessing it. As mentioned earlier, the subject name of the certificate must match the federation service name. It seems when creating a self signed cert in IIS 7.5, it will only let you create a cert that uses the server name itself for the subject. For this reason, I used SelfSSL which is part of the IIS 6 resource kit because it gives you the freedom to create a subject name of your choice. To create a self signed cert, download SelfSSL to the ADFS server and open a command prompt as administrator. Change to the directory which contains the the SelfSSL executable and type the following command replacing “adfs.pipe2text.com” with your own federation service name:
selfssl.exe /T /N:cn=adfs.pipe2text.com /V:365
Note: You may receive an error about being unable to open the metabase when running this command. You can safely ignore this error.
Using the /T will make sure the cert is place in the “Trusted Root Certificate Authorities” in addition to the “Personal” certificates on the local machine. Since Im doing this in a lab the self signed cert and not issued by a trusted 3rd party CA like Verisign, it will need to be placed in “Trusted Root Certificate Authorities” on any machine that will be accessing the service using this certificate or there will be certificate errors. The ”/V:365″ switch will make the cert valid for 365 days. You can increase this if you desire.
Now that you have your self sign cert created, you will need to bind it the default website in IIS following these steps:
1. Open the IIS Manager and right click the “Default Website” and select “Edit Bindings”.
2. Under “Type” choose “https” and under “SSL Certificate” choose the cert that was created using SelfSSL and click “OK”.
3. You will now see “https” and “443″ in the list of site bindings. Click “Close”.
Configuring the Host file on the ADFSProxy Server
Since your ADFS proxy Server will be sitting on the DMZ and needs to resolve to the same federation service name that is used for your ADFS Server Farm, you can use the local host file to have the ADFS Proxy resolve the federation service name on the ADFS Server Farm. For example, you would open the host file located in “C:\Windows\System32\drivers\etc” and add in an entry (in my case) adfs.pipe2text.com and the IP address which resolves to the internal ADFS Farm that has the federation service name of adfs.pipe2text.com. As explained earlier, you would have adfs.pipe2text.com in external DNS resolving to a public IP address pointing to the proxy server(s) on the Internet. On the internal network you would have DNS configured so that adfs.pipe2text.com resolves your internal ADFS farm. In addition, the proxy server(s) will use their local host file to resolve to the internal ADFS farm using the same name.
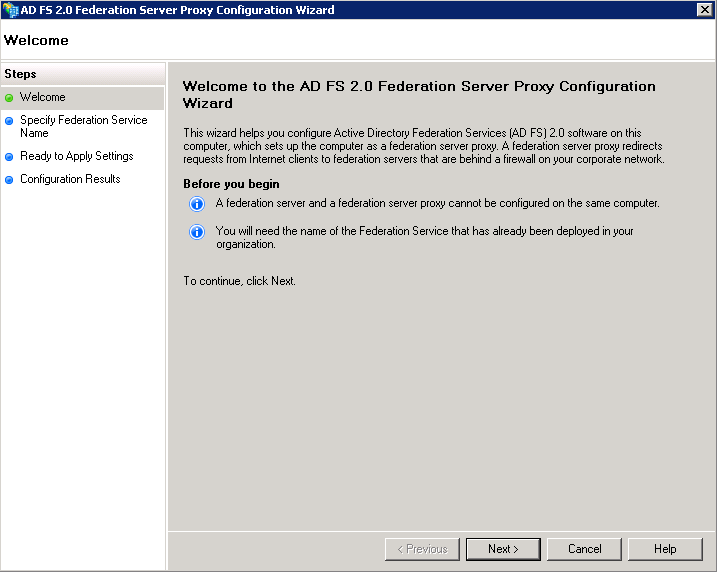
Running the AD FS 2.0 Federation Proxy Server Proxy Configuration Wizard
1. Open the “AD FS 2.0 Federation Proxy Server Proxy Configuration Wizard” from the Start Menu.
2. Click “Next on the “Welcome” screen.
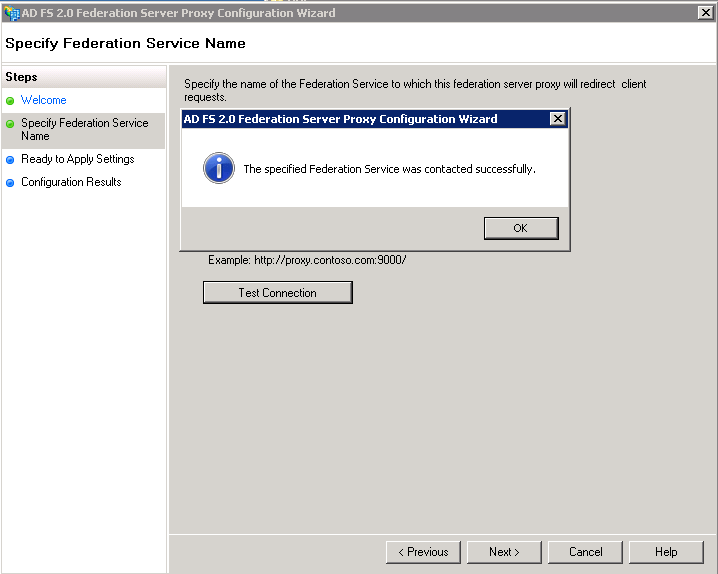
3. On the “Specify Federation Service Name” screen, enter in the federation service name and click the “Test Connection” button. If all goes well you will see a successful connection as shown below. Click “OK” and then click “Next”.
Note: If you are using a self-signed cert in a lab scenario such as I am, you will receive a certificate error and the test will fail. In this case, you would need to import the cert from the ADFS server into the “Trusted Root Certificate Authorities” of the proxy server so that it is trusted. If you are using a cert from a 3rd party CA like Verisign as you would in a production scenario, the cert will already be trusted and this wont be necessary.
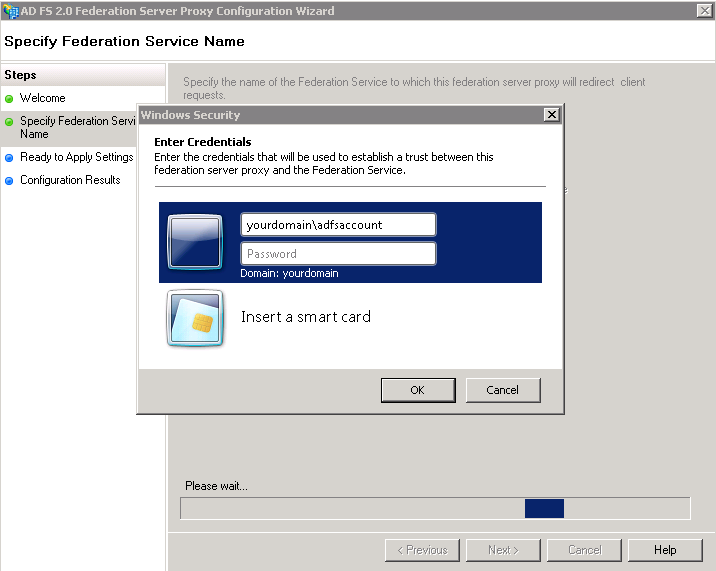
4. When you click “Next” on the “Specify Federation Service Name” screen you will be prompted for the ADFS Service account name that you used when configuring your internal ADFS Server Farm as shown below and click “OK”.
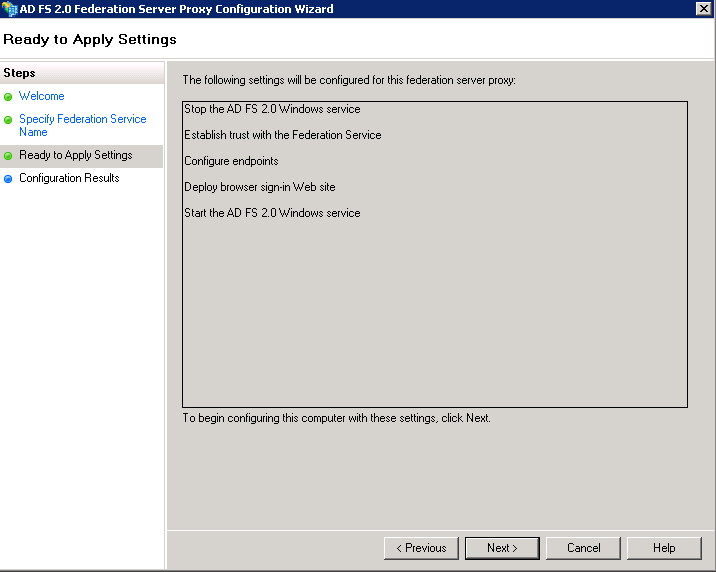
5. On the “Ready To Apply Settings” screen click “Next”.
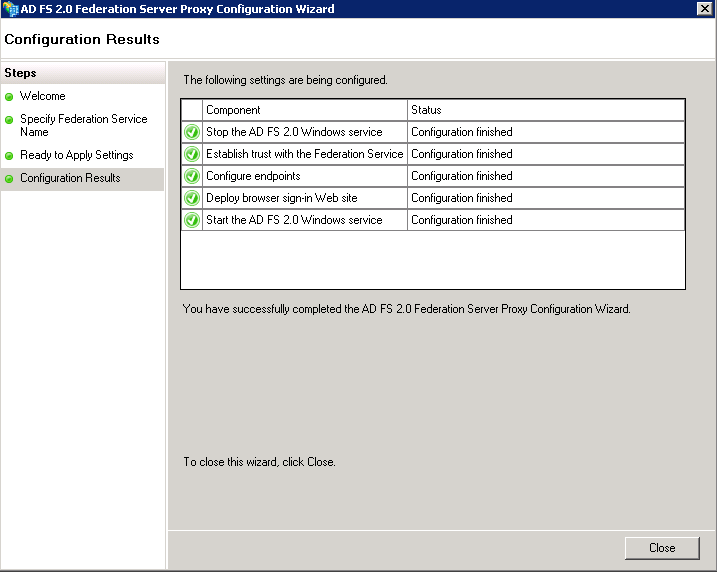
6. When everything is complete on the “Configuration Settings” screen, click “Close”.
Now your proxy server has been configured. You can repeat these steps for each additional proxy server you would want to add. For multiple proxies, you would also need a load balancer to balance the traffic. When adding additional proxies, you would also need to export the cert (with private key) from the first proxy and import it for use on the other proxies. For more information on exporting and importing certs see Adding an additional ADFS Server to your ADFS Farm when using SQL for the Configuration Database. It is possible to use the same SSL cert for your ADFS servers and your ADFS Proxies but depending on your security requirements and best practices you may want to use one cert across your proxies and another cert across your internal ADFS servers. You can go to the Technet library and do some more reading about cert requirements for more information. As always, I recommend fully testing everything in a lab scenario before rolling it out to production. I hope this helps. If you have any questions or feedback please leave a comment.
Related Links:
Installing Active Directory Federation Services (ADFS) 2.0
Configuring your ADFS 2.0 Farm to use a SQL Mirror
Adding an additional ADFS Server to your ADFS Farm when using SQL for the Configuration Database

I was very impressed by this document. I have been looking for something like this for sometime. It was very helpful and well written! It took you step by step of what needed to be done (installing and configuring ADFS proxy server) and the screen shots made it very easy. Thank you for posting. I will be checking your site on a regular basis!!! Keep up the amazing work!
This was exactly what i was looking for. Thanks a million
Great guide to ADFS. I have a question on the proxy server configuration. If we have the backend as SQL for configuration db of ADFS Service, do we have to use fsconfig.exe command line for the proxy set up as well, or can we use the built in proxy wizard to set up the proxy service even when we have ADFS using SQL as backend. Any ideas would be appreciated.
Thanks
N0 need for fsconfig for the proxy if using sql. just follow the steps in this article.
This document should be the official MS documentation, so much less convoluted! Thank you very much for taking the time to create this for us.
Thanks. Glad this blog was helpful.
This is a very well documented. My Q?, is the AD FS Proxy joined to the domain while still in the DMZ?
The ADFS Proxies are not Domain joined.
Can the ADFs Proxy be a member of a DMZ domain? Or does it have to be completely stand-alone?
Should be stand alone.
Well very written document.
Thanks great article. Any info on firewall config? only 443 to the internal FS servers?
Port 443 should be all you need. Thanks for the feedback.
Do we need ADFS proxy server at partner domain side?
Hi Vinod,
Can you please explain what you are trying to accomplish? More details will make it easier to try and answer this question. Thanks.
impressed, awesome information from all the angles.
just to know, what exactly the ADFS service we need to give? its the ADFS server site name like https://adfs.contoso.com ? no need to mention the federationmetadata?
Regards,
Sudhanshu
Hi Sudhanshu,
I would like to try and help but I need some clarification. Are you asking what the name in DNS should be?
hey tons of thanks for replying me. 🙂
I mean when you configure ADFS Proxy, we need to give the ADFS Service name rt?
so there what we will give, suppose my ADFS URL is https://adfs.contoso.com ?
and then one more Q is , my ADFS Proxy also should be same as ADFS one ?
and the same for ADFS Proxy I have register in the Public DNS rt?
Regards,
Sudhanshu
Hi Sudhanshu,
If I understand correctly, yes you would give the Federation Service Name. Also, as mentioned in the article, you need to have both the ADFS Proxies and the ADFS Server farm need to resolve to the same Federation Service Name (For example adfs.pipe2text.com). This can be accomplished by using a Split Brain DNS. Hope this helps.
Dear BC,
Thank you for your ‘Installation and Configuration Steps’ blog.
It is very useful for people, like me, who has no possibility to test it self in TestLab.
Just few questions, if you permit.
Would you please give more details or examples at some places in your blog?
At:
“AD FS 2.0 Federation Proxy Server Proxy Configuration Wizard”
On step3:
3. On the “Specify Federation Service Name” screen, enter in the federation service name…”
Should it be, as you mentioned, the SSL: “cert that uses the server name itself for the subject” Is it like: ADFS1 (host name), or FQDN: adfs1.contoso.com?
on step4:
”4. When you click “Next” on the “Specify Federation Service Name” screen you will be prompted for the ADFS Service account name…”
Should it be like a ‘host name’: ADFS1, or like a FQDN: adfs1.contoso.com?
Also, may be you can explain for me one phrase on Technet: about we need to identify which value must be included in the certificate, that is deployed to Federation Proxy Server :
“It is important to verify that the subject name in the server authentication certificate matches the Federation Service name value that is specified in the AD FS Management snap-in.”
http://technet.microsoft.com/en-us/library/dd807054.aspx
Unfortunately I cannot ask the question on this Technet page directly. I start looking for more details on internet, but every time at this point there is no details or examples are given.
Even on your helpful IT blog I haven’t found the answer.
I would appreciate your help.
Thank you in advance,
Violetta
Hi Violetta,
Federation service name would be what you decided to call the federation service name. For example, mine would be adfs.pipe2text.com. Not the server name itself. In my setup the Federation Service name is adfs.pipe2text. DNS is adfs.pipe2text.com. I have 2 ADFS proxies ProxServer1.pipe2text.com and Proxserver2.pipe2text.com behind a load balancer facing the internet resolving to adfs.pipe2text.com. On the inside, I have 2 adfs servers adfs1.pipe2text.com and adfs2.pipe2text.com also load balanced resolving to adfs.pipe2text.com. Certificate should have the federation service name, in this case adfs.pipe2text.com. Take a look at this article a it has diagrams that may help. https://pipe2text.com/?page_id=2719 Hope this helps.
Thank you, BC!
Finally it is clear now for me.
Thanks a lot!
With kind regards,
Violetta
Thanks so much for the article. Very helpful!
Hey BC, great article. Can one proxy instance handle multiple sources (IE. Vendor A, Vendor B goes to proxy A) or do you need to setup a proxy server for each source (IE. Vendor A would go to proxy A and vendor B would go to proxy B)?
If I understand correctly, the proxies are not dedicated to a vendor. They are load balanced for request.
Right, basically there is only one proxy configuration possible per ADFS implementation and its multi-use. Thanks for the timely response.
Hi BC,
Nice Initiative taken by you to answer the queries related to ADFS.
I have one query regarding the ADFS certificates.
In my ADFS setup, I have 2 ADFS servers in NLB and 2 ADFS proxy servers in NLB in Resource domain. I have 0ne ADFS server & ADFS proxy server at the partner domain.
I have generated ADFS certificate from Internal Root CA with the name say adfs.abc.local and got one SSL 3rd party certificate for ADFS proxy server with the name say adfs.xyz.com for internet DNS server.
I have configured the ADFS proxy server with the certificate that is on the ADFS server i.e. adfs.abc.local
Can you please suggest me how to configure ADFS 3rd party SSL certificate on the ADFS proxy server and how it will communicate to another ADFS proxy server on the partner domain?
Are you saying that your proxy servers are on a different domain as in active directory domain? If so, proxies are not domain joined. Also, the certificate name on both the proxy and the adfs servers must be the same (in my example adfs.pipe2text.com) which is also the same as the federation service name. Hope this helps.
Hi, thanks very much for this post, very useful and easy to follow.
One question I have, there is very little in the way of NIC requirements for proxies in the DMZ. Do the proxies need an external & internal facing NIC or can the perform the traffic routing to the federation servers?
Take a look at these diagrams and see if this helps. Thanks.
https://pipe2text.com/?page_id=2731
https://pipe2text.com/?page_id=2719
Excellent write up. Very straightforward documentation. Good job, i agree with other posters that this should be the official microsoft document for installing/configuring ADFS Proxy. Thanks to this document I was able to restore our ADFS Proxy (from a huge failure) without any problems! Thanks so much and keep it up! Site Bookmarked!