Hi all,
A very useful tool that can be used to get a better look at what is what is happening on your ADFS servers and for troubleshooting purposes is to enable security auditing for ADFS. This will log ADFS security events to the Security log in event viewer. There are easy steps that you need to take to get this working.
Step 1 – Grant the ADFS service account the “Generate security audits” right on the ADFS server. To do this, open the local security policy on the server gpedit.msc (can also be done thru GPO for multiple servers). Navigate to “Windows Settings\Local Policies\User Rights Assignment” and add the ADFS Service Account to have the “Generate security audits” right.
Step 2 – Run the following command from the command prompt:
auditpol.exe /set /subcategory:”Application Generated” /failure:enable /success:enable
Step 3 – In the ADFS console, right click “ADFS 2.0” and choose “Edit Federation Service Properties” when the “Federation Service Properties” dialogue box appears choose the Events tab and select “Success Audits” and Failure Audits” as shown below.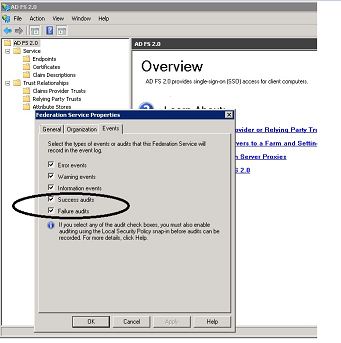
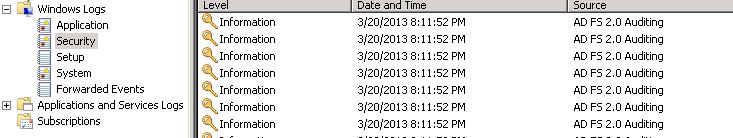
Now that you have complete the steps you will begin to see events in the Security log of the event viewer for ADFS as shown below.
You are now finished enabling ADFS Security Auditing. I hope this helps!

Getting an error on step 2. I’m running it from an elevated command prompt on Win 2008 R2. The error is:
Error 0x00000057 occurred:
The parameter is incorrect.
Hi JerkyChew
I was able to recreate the error. Try typing the command instead of copying and pasting from this site. You could also copy and paste the command into notepad and re-type the quotation marks. Then copy and paste the corrected line from notepad to the command prompt and run it. I will figure out how to correct it in the future so it can be copied and pasted directly from this page. Thanks for your feedback.
we have splunk which we feed adfs logs into.
we stopped getting logs pertaining to eventcode 299 for some reason. i think it might have something to do with some GPOs being pushed which disabled some logging settings. However, looking at ADFS properties, all the events are checked, the system account is allowed in ‘generate security audits’
When i try to verify my settings however, i get the following:
H:\>auditpol.exe /get /subcategory:”Application Generated” /r
Machine Name,Policy Target,Subcategory,Subcategory GUID,Inclusion Setting,Exclusion Setting
PTC-WCADFSAP701,System,Application Generated,{0CCE9222-69AE-11D9-BED3505054503030},No Auditing,
Can someone confirm if this means i have not set it to log audit events and if so, what am i doing incorrectly? thanks in advance.