We recently migrated over to Lync 2013. After switching all inbound and outbound connectivity to our Lync 2013 Edge servers we noticed issues between our on prem users and AOL contacts. Some AOL contacts would show updating, some would eventually show online but any IM’s sent to them would sit there and eventually fail. We did some tracing and debugging and found the fix to be the following:
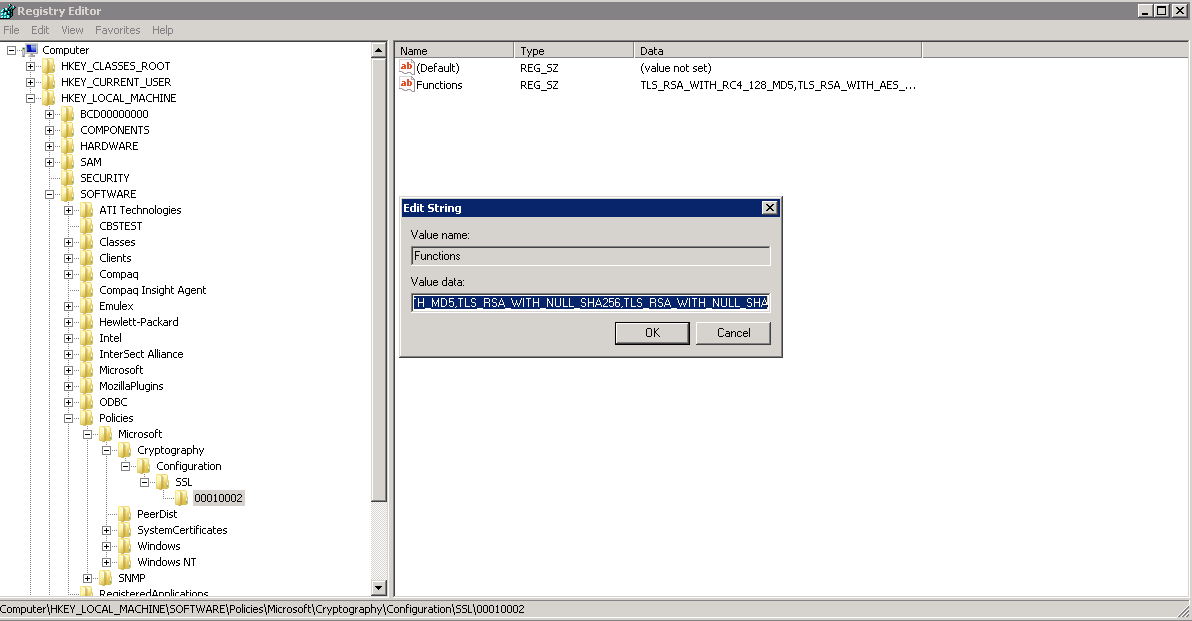
AOL connectivity requires that the SSL Cipher Suite Order on your Edge servers to be set in a specific manner. You can make this change thru GPEdit.msc but when trying this on our Edge servers we weren’t able to fit the amount of characters in the value field. So instead we modified the value in the registry. Open regedit and go to the following:
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Cryptography\Configuration\SSL\00010002
Click on functions
Copy the text in the value data field into Notepad. Search for the value below in the notepad file.
TLS_RSA_WITH_RC4_128_MD5
Copy it out and then delete it, make sure there is only one comma remaining in the section of text you’ve deleted it from. Paste it at the beginning of the notepad file. AOL requires this has to be the first one that it reads when looking thru this attribute, not sure why exactly but changing this works. Paste the update text in your notepad file back into the value data field of the registry key.
The file should look something like this when complete
TLS_RSA_WITH_RC4_128_MD5,TLS_RSA_WITH_AES_128_CBC_SHA256,TLS_RSA_WITH_AES_128_CBC_SHA,TLS_RSA_WITH_AES_256_CBC_SHA256,TLS_RSA_WITH_AES_256_CBC_SHA,TLS_RSA_WITH_RC4_128_SHA,TLS_RSA_WITH_3DES_EDE_CBC_SHA,TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256_P256,TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256_P384,TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA_P256,TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA_P384,TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA_P256,TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA_P384,TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256_P256,TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256_P256,TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384_P384,TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384_P384,TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA_P256,TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA_P384,TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA_P256,TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA_P384,TLS_DHE_DSS_WITH_AES_128_CBC_SHA256,TLS_DHE_DSS_WITH_AES_128_CBC_SHA,TLS_DHE_DSS_WITH_AES_256_CBC_SHA256,TLS_DHE_DSS_WITH_AES_256_CBC_SHA,TLS_DHE_DSS_WITH_3DES_EDE_CBC_SHA,SSL_CK_RC4_128_WITH_MD5,SSL_CK_DES_192_EDE3_CBC_WITH_MD5,TLS_RSA_WITH_NULL_SHA256,TLS_RSA_WITH_NULL_SHA
Make sure you test this out and verify all of the settings look correct, in a lab wherever possible. After completing this on your Edge servers I would recommend a reboot of each Edge server. I tried restarting Lync services but it really didn’t take effect until all Edge servers were fully restarted.